10 Cybersecurity Tips for Online Shopping: the Ultimate Checklist For Online Shoppers
2023-08-23
Online shopping has revolutionized the way we purchase goods and services. While generally safe, especially if you already practice good cyber hygiene, it also comes with risks such as scams and malware that can compromise your personal information and financial security.
Facts and Figures
Online shopping is usually a safe practice, and common sense is often enough to prevent one from falling victim to attacks on their data security. That said, there are instances where people commonly let their guard down. For example, we might put stock in larger ecommerce platforms and assume that we would naturally be safe when making purchases through them, and yet that is not always the case.
According to research published by Lloyds Banking Group, over two thirds of all online shopping scams begin on Meta-owned platforms Facebook and Instagram. This is costing shoppers in the UK over £27,000,000 per year in stolen funds. The types of scams that are used by bad actors to defraud their victims are varied, and vectors include email, SMS and even offline methods.
These scams and attacks are widespread, too. Over a fifth of Italian consumers report that they have been scammed while online shopping, making it more commonplace than impersonation scams, phishing and identity theft.
There are calls for companies such as Meta to take more accountability for the fraudulent activity taking place on their platforms, however we must make sure that we are personally taking the necessary steps to protect ourselves, too. Consider following these ten rules to ensure your own safety while online shopping.
Ten Top Tips for Safe Online Shopping
1. Stick to Trusted and Reputable Websites
While the majority of online shopping scams are taking place on social media, the major ecommerce platforms still remain relatively safe bets for your online shopping. Although it can be tempting to browse to the tenth page of Google search results and find what appears to be a genuine outlet store offering incredible discounts, doing so may make you vulnerable to fraud. Instead, opt to use platforms which are trusted, vetted and audited.
2. Be Wary of Suspicious Emails and Links
You may occasionally receive advertisements for products and services via text or email. Sometimes these can be very tempting, offering you great products or better rates than you can otherwise find online, or perhaps you are driven to jump at the opportunity by a timed discount or a limited stock - there are many methods that scammers use to give you that "Fear Of Missing Out" (also known as "FOMO"). But these are predatory tactics, not only used by genuine retailers, but scammers as well. Always be extremely careful with email attachments, and make sure you hover over links before clicking them, because a link that appears to be for one website can take you somewhere completely different. For example: https://www.whiteblueocean.com/newsroom/
3. Research the Seller
Fundamentally, this is a major problem which drives a large amount of the fraud that is taking place over social media - it is so much harder to vet the sellers that you intend to buy from. However, regardless of who you purchase from or what platform you use to do so, make sure you read around as best you can to ascertain if it is safe to do so. If the seller or store is relatively unknown, treat it with caution and see if you can find any ratings or reviews from previous buyers, but also bear in mind that these reviews may not be real in the first place. You might also be concerned if you are only offered unconventional payment methods by means to make your purchase, or if the seller’s prices are simply too good to be true.
4. Use Strong and Unique Passwords
While online shopping, you may be required to make accounts for the websites of various retailers. You must ensure not to reuse your old passwords, as credential reuse is one of the leading causes of account hacks. White Blue Ocean and the CRIF Cyber Observatory witness millions of email-password combinations enter the public domain every year, which are obtained by bad actors through a variety of methods. It is imperative that you use unique passwords for every website, which are also strong enough not to be brute-forced, and also that you change them regularly. Consider also enabling multi-factor authentication to keep your accounts as safe as possible. For more information, read our guide on password security.
5. Keep Your Devices and Software Updated
This point is particularly important for defending against malware, which can infect your system through a number of different attack vectors. When it comes to online shopping, this most likely will occur if you are required at any point to download and open some file, for example an attachment to an email or text message. Malware infects your devices by exploiting vulnerabilities in software. Software providers are obliged to provide regular updates that patch out these vulnerabilities before they can be exploited, however if you neglect to perform these updates, you leave yourself open to attack. To mitigate the risk of attack, be especially careful with downloads - check the file extension is what you expect it to be, and consider if the source of your download is safe. Additionally, make sure that you run regular or automated updates to keep your device and apps secure.
6. Use Secure Payment Methods
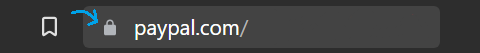
You can get by online with just a handful of payment methods: PayPal, Apple Pay and Google Pay. All of these offer the additional option to require verification for each purchase; this being an option you should strongly consider. And you will know it's secure by the small lock symbol in your address bar.
 |
|
Figure 1: Pay attention to this padlock, as it symbolises a real and genuine certificate for authenticity received from the target site. |
On a more sketchy website, they might advertise that they support these payment methods, but could offer you fake versions of them, or restrict you to only paying through manually entering your card information. This is an easy way to have your data stolen by bad actors. The key here is to remain vigilant and always ensure that you are interacting with a genuine website and in a safe manner.
7. Be Cautious with Personal Information
If a website is asking for your personal information, it can be useful to ask why. Is it completely necessary that this online retailer is requesting your date of birth, your address, the colour of your first car and the name of your first pet? Strive to provide only as much information as is necessary for the transaction, and if more is asked for, then be wary. Any personal data of yours that is obtained by a bad actor, no matter how innocuous it seems, can and might be used against you.
8. Be Mindful of Public Wi-Fi
Connecting to public Wi-Fi connections can be a dangerous activity in general, because your web browsing can potentially be monitored. Unsecured and unregulated public connections are sometimes used by bad actors as a means of mass-harvesting information from unwitting victims who might simply be looking to use less of their own mobile data. Some public connections are safe, however, but it is best to treat them with caution regardless. For that reason, you should avoid making purchases or inputting sensitive information while connected to public Wi-Fi networks. Additionally, you might like to consider utilising a VPN to further mask your online activity from unauthorised onlookers.
9. Stay Updated on Scams and Security Best Practices
This is an important step, but simply: keep an eye on the news. You will continuously learn of the latest trends in online scams, such as the infamous fake delivery SMS scam, or fraudulent emails about supposed issues with your Facebook Marketplace listing. Knowing the common scams at any given moment provides you an extra layer of protection, as it will predispose you to approach certain things with caution. If you are prepared for a scam, then you are far more likely to avoid it. In addition, browse the web and use e-commerce websites using cybersecurity best practices, for example by maintaining good cyber hygiene. These practices will make you impenetrable to attack.
10. Trust Your Instincts
If you feel that something is wrong then it may well be so. We have talked about the popular methods of scam artists, such as their exploitation of the Fear Of Missing Out and other predatory practices. Knowing this, you will hopefully recognise when it is being used against you in future. You might not remember all that you have read, but you will feel that something dodgy is afoot. Trust that feeling, and explore it, because sometimes some brief consideration and self-awareness can be all that is needed to halt you in your tracks and prevent you from divulging any sensitive information. If ever in doubt, stop and think. Use Google or another search engine to confirm or deny your suspicions. Armed with your current knowledge of scams, you should now understand and realise when one is in front of you.
Conclusion
Online shopping offers convenience and accessibility, but it's crucial to remain vigilant to protect yourself from scams and malware. Make sure to follow our tips, for a secure online shopping experience, safeguard your personal information, and enjoy peace of mind while you shop. Remember, staying informed and adopting cautious online practices are key to a safe and enjoyable shopping journey.
Sources
https://www.whiteblueocean.com/newsroom/crif-cyber-observatory-2022-yearly-report/
https://www.whiteblueocean.com/glossary/
https://www.whiteblueocean.com/newsroom/become-hack-proof-with-cyber-hygiene/
https://www.whiteblueocean.com/newsroom/password-security/
https://www.whiteblueocean.com/newsroom/a-guide-on-text-message-scams/
https://www.whiteblueocean.com/newsroom/why-phishing-emails-contain-errors/
The information contained in this article is provided for informational purposes only and does not constitute professional advice and is not guaranteed to be accurate, complete, reliable, current or error-free.

Related news

Avoid online shopping scams at Christmas
2024-12-06The risks of online scams, including imposter scams, fake deals, and malvertising, are significantly higher during the holiday season. With so many tempting offers, shoppers are often targeted by cybercriminals. Learn some simple tips for safe online shopping and safeguard your personal and financial information.
Read more
New Mishing Campaigns Target Job Seekers
2025-01-31Mishing attacks, a form of mobile phishing, are being used in recruitment scams to target job seekers. These attacks involve sending fake job offers via SMS or messaging apps, leading victims to download malware onto their devices. This article explores the rise of mishing attacks, how they work, and the steps you can take to safeguard your personal information and financial data from these threats.
Read more
Malicious Browser Extensions
2022-11-18Browser Extensions can improve the convenience, productivity, and efficiency of browsers; however, they are not always secure as they look and can pose a significant challenge to cybersecurity. As a matter of fact, extensions can be easily downloaded with just one click, typically have full access to the contents of any web page the user loads and can handle sensitive data. This has made extensions a valuable target for threat actors.
Read moreContacts
Let's talk
Please fill in the form below (fields with * are mandatory) and we will respond to your request as soon as possible!